Abstract
Integrated Risk and Compliance Frameworks for Global Data Center Operations: A Governance-Centric Approach presents an objective, evidence-based analysis through a governance-focused lens, emphasizing strategic alignment, stakeholder engagement, and measurable outcomes. Specific risk and compliance paradigms governing data center operations are identified, and the impact of these paradigms on oversight, control, and reporting is assessed. A comparative study of traditional operational controls and a governance-led compliance-centric methodology demonstrates the latter's potential to become the primary driver of data center risk and compliance. Governance encompasses the continued alignment of business goals with risk appetite, regulatory requirements, and operational capabilities; a defined structure for accountability, including oversight committees and established roles and responsibilities for risk and compliance decision rights; and a mechanism for stakeholder engagement that enables periodic and continuous validation of strategic decisions. Integrated risk management frameworks leveraging these principles are a prerequisite for effective risk and compliance management in the context of global data center operations.
1. Introduction
Data centers, the backbone of internet infrastructure and e-commerce activities, serve a multitude of purposes, including data storage, processing, and management. Risks associated with data center operations fall into multiple categories, including Operational and Physical Security, Cybersecurity, and Information Assurance. These risks can severely impact the enterprise data stored within, as well as associated functions such as Cloud and Co-location services. Effective governance is crucial for managing these risks, and a strong alignment of business objectives with appetite levels for operating and infrastructure risks—coupled with a definition of operations—can drive the Governance, Risk, Compliance, and Resilience functions effectively.
Additionally, stakeholders from Risk, Compliance, and Operations require mechanisms to engage and communicate with the business as inputs to these functions, including Data Privacy and Data Protection requirements from Regulatory authorities across jurisdictions. A clear mapping of Regulatory obligations across jurisdictions in which Data Centers operate, including cross-border jurisdictions should, be an extension on from the previous mapping exercise; this will address Data Privacy and Data Protection Obligations and considerations for cross-border Data Flows, enabling the Compliance Governance model of Data Center operators.
2. Governance-Centric Paradigms in Data Center Operations
Governance considerations shape a variety of aspects in data center or dedicated hosting operations. However, risk and compliance are typically examined via control mechanisms that seek to ensure that all aspects of the business are consistently delivered without failure, loss, or damage. Risk management principles merely serve as supporting components and are not the central driver of risk and compliance activities, even though the industry is subject to a multitude of laws and regulations covering numerous aspects of operations, technology, and the data processed within. Consequentially, the roles, responsibilities, and accountabilities of individuals and empowered bodies are rarely discussed, and operating decisions often lack transparency.
A governance-centric approach proposes that, first and foremost, business priorities should govern all undertakings, followed by the risk appetite of the business—accepting that risk cannot be eliminated. The business requirements should drive the decisions and controls deployed for the support functions, so that reputational and financial impact—manifested through loss of customers and, therefore revenue—is minimised. Thereafter, risk management principles and industry-standard control frameworks such as ISO-27001, NIST 800-53, PCI-DSS, and any executive or internal directives on information security should guide the information security operating model and controls. Finally, technology decisions should be made within the context of the adopted enterprise information security policy and risk appetite, thereby enabling a resilient architecture based on thorough threat modelling.
2.1. Strategic Alignment and Stakeholder Engagement
Both business convergence and risk appetite should align with the stakeholders’ expectations. Additionally, global regulations and local laws must be incorporated across jurisdictions. Evolving operational capabilities and vendor integrations should also be considered in achieving such alignment.
2.1.1. Stakeholder Engagement
Data center operations cover End User and Service Provider. They have their own internal organizations that include regional, security and risk departments, that should have the same Board of Directors with Data Center operation’s Board of Directors. The objective is to obtain feedback on risks and internal security needs. Based on that and regional operation needs, the Data Center Risk and Security should put together a joint presentation for reviewing and seeking approval. This approach will help in obtaining a consolidated view of both sides about security matters, risks and priorities in the centers. Additionally, process or technology changes that may impact business continuity must pass through that channel in order to receive the service provider validation.
Throughout the operation, incidents and near misses must be treated and reviewed in detail in order to improve the operation. Those must have a formal assignment of record and ownership in order to contribute to changes in readiness or processness. The information resulting of those analysis should be presented periodically for the Board of Directors in order to also get their approval towards changes that may create investments or big changes in operational processness.
2.2. Accountability Structures and Oversight Mechanisms
Accountability structures translate business risks, regulatory obligations, and risk appetite into Key Risk Indicators that provide boardroom visibility of the risk landscape. A board-level risk management committee oversees the enterprisewide risk governance process and approves the data center risk architecture. Supporting the committee are data-center-specific leadership and assurance forums encompassing operational, physical security, cybersecurity, and information assurance domains. Cross-domain risk prioritization relies on alignment, governance, and assurance resources operating globally across data center operations and facilities. Risk ownership lies with data center leaders who, along with the Information and Cloud Delivery organization, maintain decision rights in their respective governance forums.
Key Risk Indicators male the connection between enterprise risk and data center operations. Each indicator comprises business context, accountability, thresholds, and monitoring mechanisms. For example, the corporate cyber-risk appetite statement establishes qualitative tension parameters and contextualizes board-guiding KRI. The cyber-risk management organization maintains a heat map of deployment KRI that gauges compliance against the appetites underlying the heat map. In addition, the availability threshold of any data center-enabled service is set-and enforced-through the process of business service continuity planning. When the probability of reaching that threshold is breached, a senior executive of the line of business providing that service raises the matter to the attention of a Governance Forum for proper escalation.
Equation 1: Governance Alignment Index
The repeatedly says that effective governance is built from:
- strategic alignment,
- stakeholder engagement,
- accountability,
- compliance harmonization,
- resilience.
So, define the five normalized inputs:
To combine them into one governance score, use a weighted sum:
where
If all five are treated equally important:
Then:
Step-by-step example
Using the normalized scores from Table 3:
Substitute:
Add numerator:
Now divide by 5:
So, the derived Governance Alignment Index is:
or on a 5-point scale:
3. Methodology
The methodology follows qualitative and quantitative paradigms to define a scholarly foundation for the integrated risk and compliance management frameworks. Source data, including regulatory guidance, legal obligations, and authoritative group positions, inform the qualitative elements of the analysis. The architectural, cloud and hybrid design, and measurement considerations are predominantly quantitative in nature and focus on a multinational data center operator. Use of multiple perspectives and lines of inquiry strengthens the analysis by enabling triangulation of evidence and conclusions.
Qualitative and quantitative analyses occur in tandem. As the qualitatively inclined elements of the work develop addressing specific strategic management processes, the Quantitative Data Collection Instrument facilitates the gathering of data from sources internal to the organizations studied. Qualitative versus quantitative analysis are further distinguished through a formal sampling approach, although the gathering and analysis of the testing data employed for the incident lifecycles, business continuity planning, disaster recovery, measurement, metrics, and maturity assessment components therefore reflect convenience sampling considerations. Ethical considerations for qualitative research relate to the respect of interviewed persons and the determination of acceptable risk exposure to unanticipated negative consequences from their disclosures.
3.1. Research Design and Approach
Data Privacy Express is a leading privacy technology company that empowers organizations to transparently comply with comprehensive data privacy requirements. Founded in 2019, the company provides a unified platform for companies to comply with privacy requirements around the world, bridging the barrier between a company and its users.
This case study focused on the Institutional Support System for South Korea’s Data Centers and the approach by which the recommendation was derived, structured around interviews with executives as well as the initial brainstorming meeting held with key Security and Networking Services personnel. South Korea is a leading Asian host of data centers in terms of capacity, number of facilities, number of operators, share of major public cloud services, and cross-border flows. Yet data centers face increasing regulatory scrutiny. Despite these dynamics, information on the country’s key institutional drivers for data centers is limited. To address this challenge, senior officials at the Information Security and Networking Services (ISNS) division of South Korea’s National Information Society Agency (NIA)—the national agency responsible for the country’s digital transformation strategy—sought an overview of the country’s supervisory, regulatory, and operational framework for data centers, and any significant gaps that might hinder continued growth as well as send the wrong signal to market participants. The work was intended to inform a larger discussion of data privacy and security among ISNS, the Ministry of Science and ICT (MoST), and the Office of the Privacy Protector.
4. Objective of the Study
Integrated Risk and Compliance Frameworks for Global Data Center Operations: A Governance-Centric Approach's objective is to identify integrated enterprise risk and compliance governance strategies for global data center operations. Data privacy, data protection, business continuity, disaster recovery, and incident response have been addressed separately for individual data centers but require joint consideration for multinational operations. Failure to factor business decision-making—particularly risk appetite, allocated resources, and technology towards compliance obligations—impairs enterprise-wide risk-and-compliance governance. A study goal defined along these lines leads to the following hypothesis: Forward-thinking enterprises that balance growth and risk in investment decisions on people, processes, and technology will reduce risk and improve compliance efficiency.
Strategic alignment is essential for sound decision-making. It connects business goals with operational capabilities, stakeholder objectives and concerns, risk appetite, and regulatory obligations. It involves translating high-level strategy into lower-layer operating models, supported by the right quantity and quality of people, desirable technology solutions, and sufficient financial resources. The strategic oversight and enterprise risk committees maintain upward accountability for implementing enterprise strategy; subordinate organizations are answerable for all decisions and resultant risk and compliance impacts. Beyond classical accident-orientated approaches, integrated risk management focuses on systematically and holistically considering all factors affecting the continuity of operations.
4.1. Study Goals and Expected Outcomes
The research aims to develop governance-centric integrated risk and compliance frameworks for global data centre operations. The work hypothesises that establishing and embedding formal governance structures that enforce alignment between strategic business objectives, risk appetite, regulatory requirements, and operational capability decreases risk exposure and streamlines compliance activities across different jurisdictions. Governance outcomes are expected to be measured through a decrement in risk exposure, a reduction in high-risk regulatory findings, and a levelling of the resource allocation for compliance-related activities across jurisdictions.
As the scope of operations expands, so do the requirements from a risk and compliance perspective. Stakeholder groups such as customers and governments express the need for assurance that the risk posture of the operations reflects their level of concern. Consequently, multiple Senior Management and Board-level oversight committees are formed with a focus, for example, on Information Assurance, Cybersecurity, Business Continuity, or Data Protection, yet are not integrated. Activities either undertaken within the various functions or addressed across the jurisdictions parallel each other without a consolidated level of Committee visible to the broader organisation.
5. Research Summary
Integrated Risk and Compliance Frameworks for Global Data Center Operations: A Governance-Centric Approach presents an objective, evidence-based analysis through a governance-focused lens, emphasizing strategic alignment, stakeholder engagement, and measurable outcomes. It examines the nature and characteristics of governance in data center operations, discusses the differences between traditional control-centric programs and governance-led operations, argues that governance should be the primary driver for risk and compliance, and outlines the importance of a global view of operations in the consideration of risk and compliance.
Strategic alignment connects the goals of the business with risk appetite, regulatory obligations, and operational capability. Stakeholder engagement mechanisms ensure that all concerns are addressed, supported by clearly defined accountability structures that describe oversight committees and decision rights, along with the governance forums for escalation and resolution. The desired outcomes of governance initiatives guide the process; consequently, the identification of measurable success criteria is a critical activity. Delivering against those criteria provides effective evidence that the governance program is functioning as intended.
5.1. Global Data Center Risk Assessment Landscape
Defining Strategic Alignment, Stakeholder Engagement Mechanisms, Accountability Structures, and Oversight Processes; Articulating Governance Objectives and Expected Governance Benefits.
Global data center operators depend on the ability to successfully identify and manage risks across diverse operational geographies. Multinational companies face more challenges than single-country operators due to broader risk profiles, exposure to multiple regulations, and varying degrees of risk tolerance across jurisdictions. Attaining stakeholder buy-in with an integrated risk assessment process that spans the entire organization enables successful decision-making while positioning the business to respond to changing business, regulatory, and risk conditions faster and more efficiently than the competition.
A growing number of multinational operators are establishing country- and region-level risk governance forums that serve to map business priorities, appetite for risk, key regulatory requirements, and decision rights across the organization. These risk forums establish baseline priorities for ensuring that global operations remain viable, compliant, and resilient over time. The outcomes of these risk governance activities can also help inform technology investment plans and projects by clearly defining changes in the underlying risk landscape and control areas that need further strengthening.
Equation 2. Inherent Risk Score
The organize the risk landscape mainly around likelihood and impact. That naturally gives the standard inherent-risk form:
where:
- = likelihood of risk ,
- = impact of risk .
Example: Cybersecurity
Then:
So:
Example: Physical security
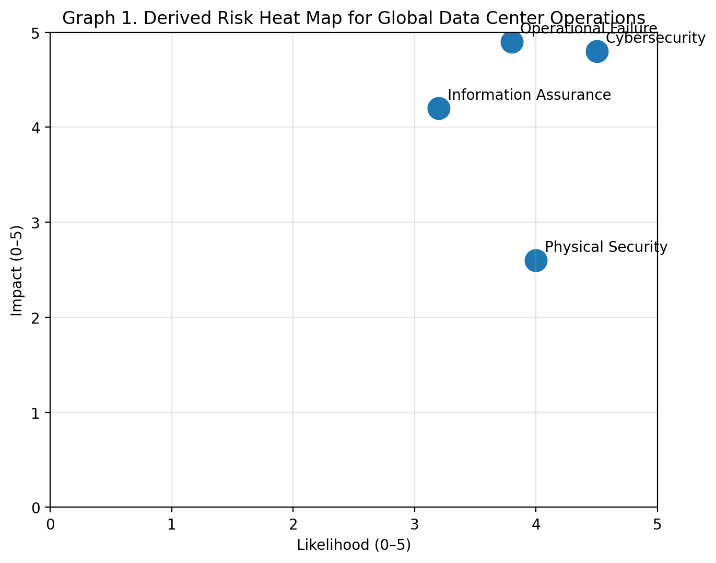
6. Risk Landscape in Global Data Centers
Risk in global data center environments falls into four broad categories: operational, physical, cybersecurity, and information assurance. While operational and physical security risks present the greatest likelihood, cybersecurity threats tend to be identified with the potential for the greatest impact. A limited set of common controls and frameworks is employed in the management of these capabilities, supported by a standard threat model. Based on these analyses, a failure event is identified that would have a catastrophic effect on continuity of service and the required resilience for the environment.
6.1. Operational and Physical Security Risks
The risk landscape for a global data center operator is dominated by the potential for operational and physical security incidents, with the likelihood and scale of impact of these incidents posing the greatest risk to the business. Operational process failures, such as loss or improper provisioning of a service, at a minimum are likely to lead to an operational impact, and may also be associated with reputational challenges. The potential for a critical incident such as operational readiness failure, business continuity failure, or serious safety incident is associated with high impact. The probability of such an event occurring at a single facility is assessed as relatively low, but the number of production facilities means that these incidents are not rare across the portfolio during a typical period of operation. Historical data regarding serious accidents in the industry indicates that this category of incident should be considered as probable, although it may not occur in every period.
Physical security events, such as forced entry to a data center, vandalism, or serious theft, are generally considered to have a high probability of occurrence but with a low impact associated with each event. Proliferation of data center assets has increased the challenge of maintaining controlled access to all sites. Physical security incidents are primarily detected by surveillance detection mechanisms, and current measures remain adequate for detection. The design of data center facilities supports mitigation, and the risk appetite simply allows for the impact associated with such events.
6.2. Cybersecurity and Information Assurance Risks
Cybersecurity threats remain a key consideration in risk governance for global data centers, as they represent the potential for events that could result in the loss of multiple client sites at the time of a single incident — indeed if not properly considered. The combination of the service model in use, the scale of attack surfaces, and increasing threat capability guarantees that these threats will continue to remain distinct at least in key global markets. The nature of these incidents is such that managements are typically obliged to tie their defenses into an industry-approved framework (for example, Submarine Cable Security Guidance for the Public and Private Sectors), and indeed threat modeling is also provided.
Information assurance requirements are also relevant for some organizations, particularly where personal data is involved. In such cases, management must also publish cyber risk insurance coverage capacity and the existence of a cyber risk national response plan, as well as measures to grant data subjects the right to a copy of their personal data in a commonly used format. These precautions tend to reinforce the basics of a secure and resilient architecture.
6.3. Operational and Physical Security Risks
Global data centers face a multitude of operational and physical security risks that threaten the integrity, confidentiality, and availability of information assets. These risks are closely monitored, and their likelihood and business impact are assessed. Mitigating controls are identified and continuously tested in situations that warrant such scrutiny. The likely occurrence and impact of risks not usually classified as audit priority are also evaluated based on management’s qualitative assessment. Information Security and Risk Management Services and Physical Security teams investigate most critical issues, including both the detection of risks and the verification of mitigation action plans. The Management Control and Risk Committees are responsible for ongoing monitoring across the entire Group according to the risk appetite and objectives correlated with Business Continuity Plans (BCP) managed at a regional level.
Disruptions of operations due to events such as natural disasters, power failures, or any other kind of breakdown in the primary or alternative data centers would lead to serious consequences, including customer dissatisfaction and contractual penalties. The likelihood of occurrence and impact are therefore classified at the highest level. The DBA teams and Corporate Security are responsible for reporting disturbances or active threats from within the Group’s facilities. Security incidents involving the Group’s business are also reported, even if they do not expose vulnerabilities in the infrastructure.
6.4. Cybersecurity and Information Assurance
Cybersecurity and information assurance risks in data center operations remain high due to the proliferation of sophisticated cyberattacks globally. Data theft and ransomware incidents have repeatedly underscored this vulnerability. Clients often demand compliance with frameworks such as ISO27001, mandated by the Payment Card Industry Data Security Standard for entities accepting card payments, and the NIST Cybersecurity Framework. Recent years have seen rising focus on standalone elements within broader data protection strategies, driven by GDPR and other legislation. Accordingly, data centers have become prime targets for advancing payment frauds. Major cloud services providers report a constant threat of unauthorized use, underscored by the escalation in cryptocurrency prices.
Cybersecurity risks extend beyond mere controls; they require a comprehensive threat model coupled with suitable security architecture for resilience and cost-effectiveness. Appropriate threat models improve incident anticipation and resilience, assisting both detective and preventive solution providers. Information assurance risks continue to gain attention across all operational domains, as escalated breaches are now leading to data integrity and availability issues. Examining risk considerations from a data center business continuity viewpoint uncovered the significant importance of data availability, manifesting in a requirement for momentary unplanned outages for a site and reduced mean time to recover in the event of data loss.
7. Integrated Risk Management Frameworks
Integrated risk management frameworks provide a robust foundation for addressing the diverse spectrum of risk in global data center operations. Commonly termed the three lines of defense, the core principles—clearly defined roles and responsibilities, system resilience, and systematic identification and assessment of risk—extend across the integrated risk landscape. Business Units, Business Support Units, and Regional Security create a nimble, efficient, and systematic environment capable of identifying and addressing operational, organizational, physical security, and relevant cybersecurity and information assurance risks. Inherent in this paradigm is a transparent, scalable, and business-focused process for assessing, prioritizing, and heat-mapping identified risk. Coupled with appropriate risk identification, assessment, and prioritization frameworks, an effective risk governance structure reduces effort overhead while enhancing risk transparency. Dedicated focus on operational and supporting units drives manageable, quantifiable, risk-based conversations across the organization.
Risk frameworks grounded in business and operating environments inherently govern not only risk management efforts but, more broadly, ensure alignment with risk appetite, support business strategy, and drive compliance with applicable requirements. Key control objectives seek risk scenarios that transcend any one BU, deploying effective controls for those that are most relevant. For those without significant relevant risk, the control environment must be sufficiently transparent to allow the business and support functions to assume ownership. Risk-related communication enables all areas to reassess areas of concern, assess residual risk, and articulate future commitments.
7.1. Framework Foundations and Core Principles
Governance governance-centric integrated risk and compliance frameworks for global data center operations underscore the importance of implementing risk and compliance regimes that support business objectives, proactive risk-taking, and governance accountabilities. Such structures enable data center operators to remain relevant by enhancing stakeholder engagement and reporting processes while responding effectively to budget constraints, operational resiliency pressures, and changing geopolitical environments. With these concepts in mind, the frameworks themselves are founded on three principles. First, risk and compliance should be consolidated within an integrated framework underpinned by established governance principles. Second, risk and compliance programs should endeavor to achieve a common set of optimal business outcomes: the capability of management and the board to make risk-aware business decisions, the enhanced satisfaction of stakeholders, and the consolidation of resources through continuous integration. Third, a common methodology should be adopted to systematically identify, assess, prioritize, and respond to risks and compliance obligations.
The integrated risk and compliance framework foundations represent strategic alignment within governance—exploiting risk and compliance as enablers of business as opposed to inhibitors to capture the economic value of risk-taking under uncertainty. The governance enablement of integrated risk and compliance programs provides a practical implementation roadmap. Recent incidents have further reinforced the business relevance of risk and compliance, creating a compelling case for change. A systematic assessment and re-engineering of the programs that support these often-quadrant activities—especially within the technology- and data-centric digital economy and its core cloud computing sectors—are long overdue, as defense is no longer sufficient. Demand for innovation and growth-oriented spending continues to be hindered by long-standing external trust deficits in the security and reliability of online services. Gartner is reportedly investing heavily in recovery, resilience, and assurance to retain its dominance in the public cloud infrastructure-as-a-service market.
7.2. Risk Identification, Assessment, and Prioritization
Systematic risk identification, assessment, and prioritization form the foundations of integrated risk management. Identification comprises cataloging threats, vulnerabilities, and resources for risk assessment. Assessment evaluates the likelihood and consequences of incident scenarios, including in-house estimates and control-based calculations. Finally, prioritized heat maps chart risks by potential impact and likelihood.
A systematic approach to risk identification, assessment, prioritization, and heat mapping supports the implementation of integrated data center risk management and ensures senior management understands the anticipated threats and vulnerabilities in global data centers. Threat modeling and assessing high-risk data center-facing services enhance the management of cybersecurity risks and strengthen the overall security posture. Business impact analysis identifies critical business operations and related maximum tolerable outage durations that inform business continuity planning and disaster recovery.
Equation 3. Residual Risk after controls
The stresses that controls, frameworks, and governance do not eliminate risk; they reduce it. So, let be control effectiveness:
Uncontrolled proportion is:
Hence residual risk becomes:
Since , substitute:
Step-by-step example: Cybersecurity
First compute inherent risk:
Next compute uncontrolled share:
Then:
So:
Step-by-step example: Operational failure
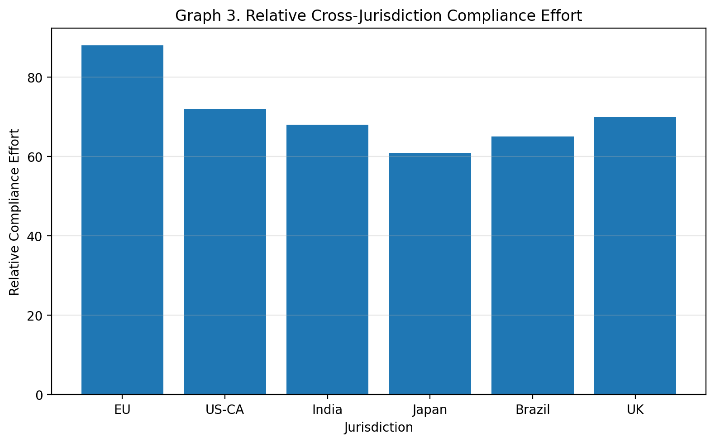
8. Compliance Governance Across Jurisdictions
Compliance governance across jurisdictions examines data privacy and data protection requirements in the context of local law obligations; the cross-border transfer of personally identifiable information; and the consent regimes defined in various privacy and data protection laws. Such requirements are mapped against the established integrated governance framework and control objectives. Similar compliance requirements across jurisdictions are subsequently identified and considered opportunities for harmonization.
Governance oversight committees and authorities within the integrated framework are responsible for managing and controlling cross-border transfers of personally identifiable information and operating within the defined consent regime. The analysis of the requirements imposed by individual jurisdictions leads to an understanding of the expectations set by regional regulators and supported by law-based processes and governance mechanisms.
Data privacy and protection laws in numerous jurisdictions are imposing increasingly stringent requirements, particularly with respect to the cross-border transfer of personally identifiable information. Compliance with such requirements enables organizations to avoid fines, sanctions, and reputational damage. Organizations that operate across multiple jurisdictions are subject to privacy and data protection legislation in each country, and noncompliance with the requirements of any one jurisdiction can result in enforcement actions by local regulators.
8.1. Data Privacy and Protection Requirements
Privacy and data protection laws and regulations are rapidly evolving along with the provisions for privacy and information protection enshrined in many jurisdictions. Furthermore, the loopholes associated with the absence of such laws are being filled at a record pace. Such developments are highly varied and are present in the various jurisdictions that the above industry operates. The European Union implemented the General Data Protection Regulation (GDPR) clamping down on unauthorized transfer of personal data outside the EU jurisdiction, imposing strict penalty for non-compliance. The GDPR promoted the concept of “The right to be forgotten” allowing individuals to demand erasure of online information associated with them. The California Consumer Privacy Act (CCPA) adopted similar provisions for the California state with additional powers such as Right to Opt-out. These were followed by similar laws in Brazil, UK, India, Japan and several others around the world. The compliance requirements necessitated organizations to integrate systems and processes to abide by the prevailing laws in the respective jurisdictions. Information technology industries and the associated data centers were also affected by this regulation where, apart from their own jurisdiction, data centers located in other jurisdictions having legislation for privacy protection needed to ensure that the data privacy and protection laws of all such jurisdictions are upheld in all transactions concerning their end-users from such jurisdictions.
Compliance to such laws requires organizations to take actions such as implementing measurement and diagnostic systems, ensuring explicit consent for data collection and usage, setting-up opt-out provisions, allowing individuals to demand erasure of online information, etc. To ensure compliance to such requirements in the data handling life cycle of an organization, systems and processes must be integrated for effectively addressing the above requirements. Such requirements for controlling the cross-border flow of data and for taking consent from end-users for the processing of their data are observed in several other jurisdictions all over the world and must be complied with by the multinational players.
8.2. Industry-Specific Regulatory Regimes
Data center service providers in sensitive business segments (e.g., telecom, finance) face additional industry-specific regulations that complement overarching data privacy and protection mandates. Governance efforts must thus ensure compliance with these specialized requirements, especially when located in multiple jurisdictions. However, variation in sectoral rules presents harmonization challenges for cross-border data flows. Inconsistency can also obstruct acquisitions, cloud provider selection, and certification procurement, so governance structures should enable effective establishment and management across the affected domains.
Industry-specific regulations often enforce heightened data protection measures, recognizing the gravity of breaches. Government agencies usually impose these requirements onto themselves, but third parties—most commonly data center service providers—must comply as well. Financial institutions and telecom network operators serve as primary examples of sectors with sector-specific mandates for stringent security controls. These regulations are elucidated in the country-specific analysis [1].
9. Resilience, Continuity, and Incident Response
Business continuity planning, disaster recovery, and incident lifecycle management must align with all-seeing stakeholder governance to ensure that management actions have the coinciding authority and support required for success. Recovery strategies for business continuity and disaster recovery should align with management-specified recovery objectives for compromising technology-related business disruptions, and should be appropriately documented, communicated, and governanced. For incident detection, containment, and recovery, action plans and assignments must reflect the requirements of technology stakeholder governance, while remaining as comprehensive and detailed as possible. Finally, the incident life cycle—for incident preparation, detection and analysis, containment, eradication, and recovery, and confirmation of closure—must incorporate decisions that require stakeholder governance oversight, as well as a post-incident review and follow-up of change actions [2].
Business continuity planning (BCP) and disaster recovery (DR) ensure that management-approved strategies exist for addressing technology-related business disruptions that extend beyond the capacity for owner-operator management recovery, as well as for enabling planned technology changes. Technology areas typically include, but are not limited to, business operations (e.g., applications, data repositories), connectivity (network), infrastructure hosting (physical and virtual), and development environments. Strategies to govern restoration of business operations are generally documented in a business continuity plan, while strategies for governing restoration of technology support services are incorporated within IT service continuity planning. Test schedules, reports, roles, and responsibilities must be governed in accordance with business stakeholder requirements for technology-related business continuity and technology supply-related recovery [3].
9.1. Business Continuity Planning and Disaster Recovery
Resilience architecture encompasses business continuity planning (BCP) and disaster recovery (DR) strategies to ensure reliable and timely resumption of critical services in case of unforeseen events. The objective is to recover and restore services in a manner agreed upon by governance structures, limiting tolerable disruptions to business functions [4].
Business continuity planning and disaster recovery encompass the processes and procedures required to ensure the timely and reliable resumption of critical services following an unforeseen incident. The aim is to recover and restore services in accordance with the objectives approved by governance and reflected in business recovery requirements, preventing situations where business functions cease to operate or where loss during downtime exceeds tolerable boundaries [5].
While business continuity planning focuses on maintaining mission and business-essential functions during an emergency, natural disaster, or act of war, disaster recovery addresses restoring the technological infrastructure and services anew. Business continuity plans identify and prioritize critical business processes and associated risks, supported by information technology (IT) systems, elements, and resources essential for the performance of critical functions. Approved plans enable the organization to respond effectively, consider alternatives, and mitigate potential loss [6].
9.2. Incident Detection, Containment, and Recovery
Incident detection, containment, and recovery processes in data centers focus on continuous monitoring, effective response, and lessons learned, aligning with key control objectives for data center availability, security, and compliance [7]. Data centers, having transitioned from being solely business enablers to direct revenue generators, demand additional layers of protection and strict adherence to abuse prevention policies by data center operators. Thus, stakeholders in data centers invest in advanced monitoring systems, including smart network intrusion detection and prevention systems, log management and intrusion detection systems, vulnerability assessment scanners, and data-loss prevention systems to ensure high-quality services [8].
The incident lifecycle encompasses preparation, detection and analysis, containment, eradication and recovery, and post-incident activity. Incorporating standard crisis management procedures and a strong monitoring infrastructure, which continuously oversees system and application logs as well as network traffic, can help contain most security incidents during detection. The containment strategy, therefore, can include isolating the impacted segment from the remaining network to protect unaffected areas while negating any reputation damage caused by the incident. In the recovery stage, system integrity, performance, and data availability are restored, concurrently ensuring that all precautionary measures have been taken to avoid future occurrences. The lessons learned phase enables organizations to examine the reasons behind the incident as well as the evaluation, effectiveness, and efficiency of incident response, thereby identifying room for improvement.
10. Technology and Architectural Considerations
Mitigating physical and administrative hazards while achieving compliance poses a challenge for data-center infrastructure design. Specific design principles help address these hazards in an integrated manner, while cloud and hybrid deployments require additional considerations. With the right approach, compliance with internal and external requirements can enhance security, stability, and cost-effectiveness [9].
The security and compliance requirements of a data center have to be considered in its design and operational controls. Segmentation, restriction of access to critical environments, and security monitoring capability are key principles of a secure and compliant data center design. These principles enhance the mitigation of risks arising from people, facilities, and other physical environments while allowing for cheaper compliance with regulations that require more stringent access restrictions.
In the case of public cloud infrastructure and hybrid sourcing/deployment models with third-party vendors or corporate entities, the governance framework must mandate both operational and architectural conditions covering all aspects of the service. Vendor risk assessment processes that adequately cover operational and architectural risk are essential, along with addressing data localization and intercloud data exchange and labor [10].
10.1. Data Center Design for Security and Compliance
Data centers must be designed with inherent security and compliance considerations to serve as resilient, reliable infrastructures for applications meeting stringent security assurances. Such designs involve data center architecture and logical constructs supporting security and compliance requirements. Data center segmentation, access controls, and auditability during design-time, deployment-time, and operation-time—spanning the system development life cycle—empower controls for safeguards mandated by security and privacy third-party certifications and/or regulations [11].
Logical data center design mandates regulatory-strict data storage and processing locale, data access controls (consent management), and restriction of external data processing (transfer) jurisdiction to those considered privacy regulatory-equivalent [12]. Physical data center design must ensure separation of resources (hardware, tenant consumption, etc.) to restrict residual data leak risk and limit unauthorized access to customer resources, thus enabling logical access control mandates—segregation of duties—enforced by auditability of operations/actions associated with that segregation [13]. Controls identify when untrusted parties, with access for operation and maintenance of infrastructure resources, handled sensitive data of the hosted systems; for those situations, assumptions of privileged access and "malicious insider is always a concern" apply and must influence the security posture for those tenant systems, such as the assurance and threat model of the hosted systems [14].
Cloud deployments, while efficiently leveraging the physical consolidation of resources, introduce vendor risk for data processing by non-regulatory-equivalent jurisdictions; this risk must be mitigated with sufficient auditing over the mitigating measures and sufficient insurance to minimize impact in the case of a potential breach or incident. Hybrid deployments could be an expedient solution for specific types of data and applications through sensible use of considered trust assumptions of the third-party services [15].
Equation 4. Total Enterprise Residual Risk
The treat the global data center portfolio as a combined governance problem. So total residual risk across all major categories is the sum:
For the four categories:
Using Table 2:
Add step by step:
Hence:
10.2. Cloud and Hybrid Deployments within Governance Constructs
Cloud and hybrid deployments are governed by the same principles that underpin the data protection, data privacy, and industry-specific regulations considered earlier. However, vendors and their locations may expose the organization to new technology-related risks [16]. Hence, rules relating to localization and specific contractual provisions addressing risk shall normally be required. When appropriate, a thorough vendor risk evaluation should be performed. Such evaluation may also extend to public cloud service providers. It must also be recognized that cloud environments generally reduce the organization's level of control, even when appropriate governance is applied, and that formal audits of vendor-provided services may not always be possible. Consequently, organizations are advised to exercise caution when migrating production services onto public clouds [17]. Public clouds should normally be used to host non-production environments where easily controllable data are stored. The organization's business continuity plan should require an identical recovery environment within a geographically distinct region, segregated at the infrastructure level from the production environment [18].
That said, the elasticity and economy of public clouds may make them appropriate platforms for hosting reserve, or fail-again resources that are used when the organization's production resources are severely degraded or completely impaired, even for extended periods of time [19]. Cloud deployments that reorganize computers into information containers may also have significant advantages over static computing environments when considered solely from a business continuity point of view. A hybrid approach using both private and public clouds may also be valid as long as the aforementioned risks are carefully considered [20].
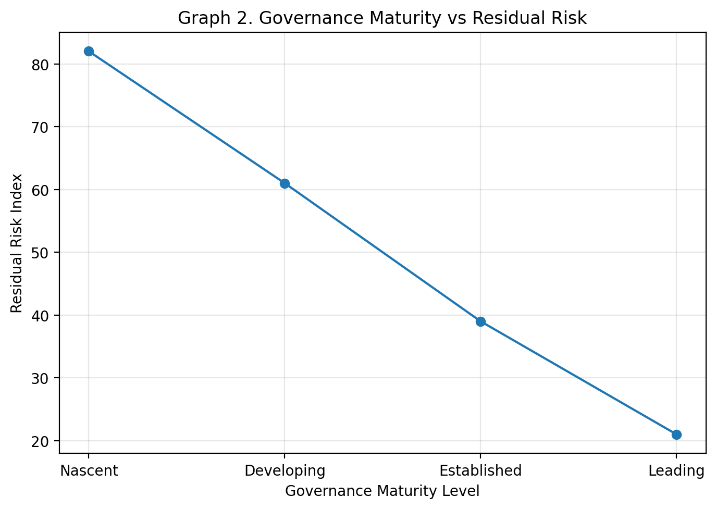
11. Measurement, Metrics, and Maturity Assessment
The success of integrated risk and compliance management systems for global data center operations is contingent on three fundamental requirements, namely, stakeholder buy-in, roadmap and prioritization of initiatives, and allocation of adequate resources. Beyond these enablers, the governance of risk and compliance encompasses measurement and metrics, maturity assessment and monitoring by means of Key Risk Indicators (KRI), compliance metrics, and a maturity assessment model [21].
A variety of quantitative and qualitative metrics enable ongoing measurement of risk conditions and compliance status. These metrics form the basis for periodic dashboards, aligned to governance oversight meetings, and for Risk and Compliance Steering Committee and Governance Body reporting. The prioritization of Key Risk Indicators (KRIs) considers the potential impact that the indicators could have on the business if the corresponding risks materialized [22]. For each KRI, the trend, indication, attribution, and alerts are assessed. In addition to the KRIs, metrics to monitor compliance with privacy requirements and processes are defined. A maturity assessment model supports the ongoing improvement of integrated risk and compliance governance and enables risk and compliance staff to work towards risk and compliance management maturity on a priority basis [23]. The maturity model may also be used to benchmark data center operations against industry peers within the same sector and serving the same client verticals and customer needs. A roadmap for building a mature integrated risk and compliance governance capability encompasses a prioritization of the available options based on impact, effort, attractiveness, and dependencies [24].
11.1. Key Risk Indicators and Compliance Metrics
Key Risk Indicators (KRIs) measure specific risk areas, including operational health, capacity for incident response, and ability to comply with regulations. They focus on first-order risks, monitoring conditions that tend to escalate risk exposure. For instance, the availability of qualified personnel is a KRI for the risk of failure to maintain system integrity, and the number of active security certifications in the organization is a KRI for the risk of having outdated or unverified standard operating procedures [25].
Compliance Key Results Indicators (KCRIs) measure actual compliance status against regulatory or contractual requirements. Regular compliance assessments should cover the level of success of remediating identified non-compliance issues and the percentage of systems and components tested under the incident response process within the defined frequency [26]. Other examples include the number of service-providing organizations whose public-certified standards were completed in the required time and the number of incidents detected and mitigated within the time period defined by the incident response plan. The established cadence of reporting and the link to governance dashboards also help to determine the criticality of monitoring these metrics [27].
11.2. Maturity Models and Benchmarking
Integrated maturity models enable assessment of governance alignment across multiple dimensions. Maturity baselines support roadmapping, resource prioritization, and the identification of governance gaps and shortcomings that risk, compliance, and business efficiency decisions do not address. The maturity model applied for integrated risk and compliance governance builds on a published data privacy and protection maturity framework, enabling the assessment of cross-border data flow safeguards, and measures the establishment of governance for integration rather than the level of control implementation itself. Maturity is classified as Nascent, Developing, Established, or Leading [28].
Benchmarking against an industry expert establishes best practices that improve governance alignment and integrate risk and compliance measures for communication, business impact, and stakeholder buy-in. The information security benchmarking framework—rooted in the international controls and compliance landscape, the national budget constraint and funding deprivation phenomenon, the growing active virtual exposure, and an industry leader’s security operational and financial commitment—is used to compare topical security areas across a range of verticals [29].
12. Case Studies and Comparative Analyses
Multinational operators manage global footprints spanning multiple jurisdictions. Data center operators handle substantial volumes of sensitive data and may therefore be especially impacted by the evolving regulatory landscape. Cross-border data flows are a regional priority, and differing jurisdictional requirements pose challenges for both customers and service providers. Responsive governance regimes that account for risk, growing data protection legislation and expectations for industry-specific regulation are viewed as key to success [30].
Governance models across a number of multinational data center operators were compared as a means of understanding challenges, best practices and lessons learned. Subsequently, a specific cross-border use case was examined to explore jurisdictional differences, areas of difficulty and possible governance-based solutions [31].
12.1. Multinational Data Center Operators
Multinational operators maintain global data center footprints, providing supporting infrastructure for various industries. Shared storage and compute facilities typically support large enterprises engaged in online transactions or service delivery. Primary geographical regions of concern usually include North America, Europe, and Asia, with foreign data center presence reducing latency in cross-border access. Governance-related challenges arise from subconnections or cross-border flows, particularly in industries subject to stringent regulation. A more focused governance-centric analysis specifically addressing multinational operators desired [32].
Successive risk-related analyses leveraged survey data comparing shared and proprietary operators. Within the high-level risk assessment and joint operational assurance study, survey respondents ranked various risks via different operational modes; the assessment also outlined response strategies and directions. In the cross-border data flow examination, governance features were compared across regulatory regimes. These studies pointed to follow-up questions requiring subsequent attention and the need for broader application of the different findings [33].
12.2. Cross-Border Data Flows and Jurisdictional Challenges
Governance of cross-border data flows is entwined with jurisdictions that impose legal and regulatory obligations concerning the location of data and its transfer across borders. Understanding these jurisdictional constraints is necessary for operators that carry, host, or process data for other businesses, particularly those that span multiple countries or regions—a phenomenon that is becoming more prevalent as businesses pursue higher quality and lower-cost solutions [34]. Consequently, cloud computing and hybrid offerings have emerged, encompassing solutions based on third-party service providers as well as those utilising internal resources and localisation of specific workloads or sensitive datasets, depending on the adequacy of the regional service provider’s offer in relation to the overall business strategy and needs [35].
Governance of these cross-border data flows focuses on addressing jurisdictional impediments in order to maximise the potential of data centres. Operator practices vary significantly, owing to the nature of both their businesses and the jurisdictions imposing requirements. To explore these impacts, a comparative assessment of governance models applied by three multinational operators was conducted. Best practices and useful lessons were extracted, as well as considerations relevant for operators, clients, and public authorities in determining feasible conditions under which cross-border data flows can take place [36].
13. Results
Stakeholder engagement, development of implementation roadmaps, resource allocation aligned with risk appetite, governance framework enablement, and effective change management are vital components for establishing a successful and functional global integrated risk and compliance governance process. The proposed integrated risk and compliance management framework enhances stakeholder buy-in, enables a clearly articulated roadmap linked to required resources, and aligns all decision-making across data centers and cloud deployments in accordance with the stated risk appetite of the data center support organization [37].
Important objectives in the process include the establishment of the governance oversight framework, the selection of an appropriate governance model for the cloud deployment, and a review of the wider integrated risk lifecycle, including the identification of Key Risk Indicators (KRIs), the generation of a risk heat map, and a general maturity assessment for compliance. Although the change program is just beginning, the initial phases have gone according to plan and are expected to yield a positive return [37]. The implementation road map highlights the priority initiatives that will provide the greatest return on investment and reflects the feedback obtained from internal and external stakeholders. Furthermore, the enabling activities that will facilitate the successful rollout of the governance approach and associated change activities are essential for gaining the confidence of all parties, both internal and external, and for ensuring productive engagement and cooperation of all interested parties [38].
13.1. Stakeholder buy-in, Roadmapping, and Resource Allocation
Integral to the success of a governance-focused data center risk and compliance framework is obtaining stakeholder buy-in. Making stakeholders aware that multiple risk and compliance aspects apply to data centers—and that such aspects require collating, analyzing, decision-making, and resolving—may seem self-evident—yet, businesses have failed to recognize the strategic importance of global data center risk and compliance [39]. In the past decade, regulators have ramped up focus on stringent risk and compliance frameworks imposed upon global businesses, which must integrate risks and compliance across multiple jurisdictions and business units. Data centers must also integrate risk and compliance horizontally across regions, and vertically aligned with business objectives and risk appetite—all supported by adequate resources. Anti-bribery standpoints of business partners and other third parties must be consolidated into a corporate-wide governance framework. That these and other data center focal points cannot be prepared in isolation but supported by business governance is both self-evident and frequently overlooked [40].
Creation of a detailed resource roadmap represents a key by-product. Roadmaps link a list of initiatives created during the stakeholder engagement exercise with prioritized resource requirements, covering built-out, continue, and renew/divest in-turn-to-actions. In the absence of resources, appropriate large—and small—investment decisions become increasingly challenging. Projects supportive of data center risk and compliance governance, such as supporting business appetite, continue to appear less important. With a long-running governance framework, along with clear day-to-day risk and compliance processes, future investment business cases present convincing proposals to business executives. Reporting against Key Risk Indicator dashboard coordinate short-term risk resolution, while risk-and-compliance-supportive operational-input templates provide governance track records justifying activity creation and funding [41].
Equation 5. Compliance Harmonization Score across jurisdictions
The discussions are mapping privacy and protection obligations across multiple jurisdictions and finding common requirements. Let:
- = total obligations in jurisdiction ,
- = total obligations in jurisdiction
Then the jurisdiction-level harmonization ratio is:
If there are jurisdictions, overall harmonization is the average:
Example derivation
Suppose 4 jurisdictions have:
- Jurisdiction 1:
- Jurisdiction 2:
- Jurisdiction 3:
- Jurisdiction 4:
Then:
Now simplify each fraction:
So:
Add:
Now divide:
13.2. Governance Enablement and Change Management
Stakeholder communications, workshops, and feedback during the previous phases of the study positioned risk and compliance decision-making within a governance framework. Action-oriented roadmaps, budgetary estimates, and roadmap resource allocation decisions addressed stakeholder concerns and generated stakeholder buy-in. Action recommendations established a strategic direction for building the workforce, skills, and capabilities within an environment of contextual, cognitive conflict. A structured change management framework supported these decisions, linking interpersonal dynamics and program conditions to outcomes [42].
Stakeholder validation confirmed the recommended governance framework, and an enabled stakeholder buy-in became the foundation for the roadmap components. Business operations, technology and application development roadmaps, and resource budgets supporting data center operations in the enterprise environment now include these recommendations, which further enable improvements in risk mitigation and compliance through reduced effort and resource intensity [43].
Consistent progress toward the integrated risk and compliance position is expected to result in associated benefits, including demonstrable ROI. Significant business benefits from changes in risk and compliance capability are anticipated within a three- to five-year period, with interim benefits reported biannually. Templates, QAI, Automated Control Testing, Technology-Supported Capability Assessment, Internal Audit, and management assessments form the basis of quantitative progress monitoring, and qualitative reporting against other aspects of risk and compliance continues in harmony with governance oversight [44].
14. Conclusion
Integrated Risk and Compliance Frameworks for Global Data Center Operations: A Governance-Centric Approach presents an objective, evidence-based analysis through a governance-focused lens, emphasizing strategic alignment, stakeholder engagement, and measurable outcomes. Operating within risk appetite, fulfilling regulatory obligations, and establishing robust oversight processes are prerequisites for achieving business goals, sustaining stakeholder relationships, and achieving reliable data center operations. Governance plays a pivotal role in these endeavours, forming the basis for risk assessment, mitigation decision-making, and operational prioritization and resource allocation.
To achieve a mature integrated risk and compliance framework aligned with business strategy, engaging stakeholders from across the enterprise is critical. The research draws on case-study and comparative analyses of multinational data centre operators, the findings—including enabling the governance functions, obtaining stakeholder buy-in and resource allocation, risk-reduction roadmaps, and improved compliance—support, and clarify the rationale for governance. Integrating risk avenues, developing organisational structures, or establishing oversight mechanisms has a quantifiable business impact, such as ROI or total cost of ownership (TCO). Supporting this level of detail remains an important aspect for applying the central findings of an integrated risk and compliance framework aligned with business strategy.
Quality is the final part of successful data centre operations, fulfilling organisational business models and health. While ensuring the requirements are fulfilled, the ability to enable and define the conditions in which the delivery platform can operate is the real benefit of having an integrated risk and compliance framework underpinning the operations. Measurement of QOS-based criteria that may impact the business is part of the governance discussion and must be defined to enable the successful business relationship with clients. An integrated risk and compliance framework helps to align all elements into a single source of requirements supporting operations and interacting with all stakeholders, from consumers of data services to the data centre management.
References
- Aitha, A. R. (2021). Dev Ops Driven Digital Transformation: Accelerating Innovation In The Insurance Industry. Available at SSRN 5622190.
- Pandiri, L., Singireddy, S., & Adusupalli, B. (2020). Digital Transformation of Underwriting Processes through Automation and Data Integration. Global Research Development (GRD) ISSN, 2455-5703.[CrossRef]
- Kummari, D. N. (2021). Smart Infrastructure Auditing: Integrating AI to Streamline Manufacturing Compliance Processes. Journal of Interna-tional Crisis and Risk Communication Research, 168-193.
- Amistapuram, K. Energy-Efficient System Design for High-Volume Insurance Applications in Cloud-Native Environments. International Journal of Innovative Research in Electrical, Electronics, Instrumentation and Control Engineering (IJIREEICE), DOI, 10.
- ADUSUPALLI, B., PALETI, S., & SINGIREDDY, S. Deep Ledger Guardians: Credit Monitoring, Insurance Risk, and AI-Driven Financial Advice on a Secure Data Backbone. JEC PUBLICATION.
- O'Mahony, N., Murphy, T., Panduru, K., Riordan, D., & Walsh, J. (2016, December). Machine learning algorithms for process analytical technology. In 2016 World Congress on Industrial Control Systems Security (WCICSS) (pp. 1-7). IEEE.[CrossRef] [PubMed]
- Meda, R. (2021). Digital Infrastructure for Predictive Inventory Management in Retail Using Machine Learning. International Journal of Advanced Research in Computer and Communication Engineering (IJARCCE), DOI, 10.[CrossRef]
- Paleti, S., Singireddy, J., Dodda, A., Burugulla, J. K. R., & Challa, K. (2021). Innovative financial technologies: Strengthening compliance, secure transactions, and intelligent advisory systems through ai-driven automation and scalable data architectures. Secure Transactions, and Intelligent Advisory Systems Through AI-Driven Automation and Scalable Data Architectures (December 27, 2021).[CrossRef]
- Inala, R. (2021). A New Paradigm in Retirement Solution Platforms: Leveraging Data Governance to Build AI-Ready Data Products. Journal of International Crisis and Risk Communication Research, 286-310.
- Mahesh Recharla, (2020), "Targeted Gene Therapy for Spinal Muscular Atrophy: Advances in Delivery Mechanisms and Clinical Outcomes", International Journal of Science and Research (IJSR), 9(12), 1921-1934. https://dx.doi.org/10.21275/SR20126161624, https://www.ijsr.net/getabstract.php?paperid=SR20126161624.[CrossRef]
- Botlagunta, P. N., & Sheelam, G. K. (2020). Data-Driven Design and Validation Techniques in Advanced Chip Engineering. Global Research Development (GRD) ISSN, 2455-5703.
- Pamisetty, V. (2021). Integrating Predictive Analytics and IT Infrastructure for Advanced Government Financial Management and Fraud Detection. Available at SSRN 5275676.
- Valiki, D., & Kummari, D. N. (2021). Rule-Based Decision Systems for the Automation of Audit Sampling. International Journal of Emerging Trends in Computer Science and Information Technology, 2(4), 105-114.[CrossRef]
- Singireddy, S., & Adusupalli, B. (2019). Cloud Security Challenges in Modernizing Insurance Operations with Multi-Tenant Architectures. International Journal of Engineering and Computer Science, 8, 12.[CrossRef]
- Botlagunta Preethish Nandan, "Data Analytics-Driven Approaches to Yield Prediction in Semiconductor Manufacturing," International Journal of Innovative Research in Electrical, Electronics, Instrumentation and Control Engineering (IJIREEICE), DOI 10.17148/IJIREEICE.2021.91217.
- Pamisetty, V. (2021). Enhancing Government Fiscal Impact Analysis with Integrated Big Data and Cloud-Based Analytics Platforms. Journal of Artificial Intelligence and Big Data, 1(1), 1-24. https://doi.org/10.31586/jaibd.2020.1339.[CrossRef]
- Aitha, A. R. (2021). Optimizing Data Warehousing for Large Scale Policy Management Using Advanced ETL Frameworks[CrossRef]
- Inala, R. Designing Scalable Technology Architectures for Customer Data in Group Insurance and Investment Platforms.
- Meda, R. (2020). Designing Self-Learning Agentic Systems for Dynamic Retail Supply Networks. Online Journal of Materials Science, 1(1), 1-20.[CrossRef]
- Sheelam, G. K., & Nandan, B. P. (2021). Machine Learning Integration in Semiconductor Research and Manufacturing Pipelines. International Journal of Advanced Research in Computer and Communication Engineering (IJARCCE), DOI, 10.[CrossRef]
- Pamisetty, V. (2020). Optimizing Unclaimed Property Management through Cloud-Enabled AI and Integrated IT Infrastructures. Universal Journal of Finance and Economics, 1(1), 1-20.[CrossRef]
- Inala, R. (2020). Building Foundational Data Products for Financial Services: A MDM-Based Approach to Customer, and Product Data Integration. Universal Journal of Finance and Economics, 1(1), 1-18.[CrossRef]
- Gadi, A. L., Gadi, A. L. Kannan, S., Kannan, S. Nandan, B. P., Nandan, B. P. Komaragiri, V. B., & Komaragiri, V. B. (2021). Advanced Computational Technologies in Vehicle Production, Digital Connectivity, and Sustainable Transportation: Innovations in Intelligent Systems, Eco-Friendly Manufacturing, and Financial Optimization. Universal Journal of Finance and Economics, 1(1), 87-100. https://doi.org/10.31586/ujfe.2021.1296.[CrossRef]
- Gottimukkala, V. R. R. (2020). Energy-Efficient Design Patterns for Large-Scale Banking Applications Deployed on AWS Cloud. power, 9(12).
- Mangala, N. (2021). CI/CD Pipeline Automation for Enterprise Data Artifacts Using Azure DevOps. Universal Journal of Business and Management, 1(1), 1-18. https://doi.org/10.31586/ujbm.2021.1363.[CrossRef]
- Kolla, S. K. (2021). Designing Scalable Healthcare Data Pipelines for Multi-Hospital Networks. World Journal of Clinical Medicine Research, 1(1), 1-14.[CrossRef]
- Mukesh, A., & Aitha, A. R. (2021). Insurance Risk Assessment Using Predictive Modeling Techniques. International Journal of Emerging Research in Engineering and Technology, 2(4), 68-79.[CrossRef]
- Mangalampalli, B. M. (2021). Scalable Data Warehouse Architecture for Population Health Management and Predictive Analytics. World Journal of Clinical Medicine Research, 1(1), 1-18. https://doi.org/10.31586/wjcmr.2021.1378.[CrossRef]
- Segireddy, A. R. (2020). Cloud Migration Strategies for High-Volume Financial Messaging Systems.[CrossRef]
- Davuluri, P. N. (2020). Event-Driven Architectures for Real-Time Regulatory Monitoring in Global Banking.[CrossRef]
- Kolla, S. K. (2021). Architectural Frameworks for Large-Scale Electronic Health Record Data Platforms. Current Research in Public Health, 1(1), 1-19.[CrossRef]
- Mangala, N. (2021). Optimizing Large-Scale ETL Pipelines Using Medallion Architecture on Azure Data Lake. Journal of Artificial Intelligence and Big Data, 1(1), 1-20. https://doi.org/10.31586/jaibd.2021.136.[CrossRef]
- Gottimukkala, V. R. R. (2021). Digital Signal Processing Challenges in Financial Messaging Systems: Case Studies in High-Volume SWIFT Flows.[CrossRef]
- Amistapuram, K. (2021). Digital Transformation in Insurance: Migrating Enterprise Policy Systems to .NET Core. Universal Journal of Computer Sciences and Communications, 1(1), 1-17.[CrossRef]
- Kolla, S. H. (2021). Rule-Based Automation for IT Service Management Workflows. Online Journal of Engineering Sciences, 1(1), 1-14.[CrossRef]
- Chava, K., Chakilam, C., Suura, S. R., & Recharla, M. (2021). Advancing Healthcare Innovation in 2021: Integrating AI, Digital Health Technologies, and Precision Medicine for Improved Patient Outcomes. Global Journal of Medical Case Reports, 1(1), 29-41.[CrossRef]
- Davuluri, P. N. Event-Driven Compliance Systems: Modernizing Financial Crime Detection Without Machine Intelligence.
- Pamisetty, A. (2021). A comparative study of cloud platforms for scalable infrastructure in food distribution supply chains.
- Kolla, S. (2019). Serverless Computing: Transforming Application Development with Serverless Databases: Benefits, Challenges, and Future Trends. Turkish Journal of Computer and Mathematics Education (TURCOMAT), 10(1), 810-819.[CrossRef]
- Davuluri, P. N. (2020). Improving Data Quality and Lineage in Regulated Financial Data Platforms. Finance and Economics, 1(1), 1-14.[CrossRef]
- Yandamuri, U. S. (2021). A Comparative Study of Traditional Reporting Systems versus Real-Time Analytics Dashboards in Enterprise Operations. Universal Journal of Business and Management.[CrossRef]
- Botlagunta Preethish Nandan. (2021). Enhancing Chip Performance Through Predictive Analytics and Automated Design Verification. Journal of International Crisis and Risk Communication Research, 265–285. https://doi.org/10.63278/jicrcr.vi.3040.
- Pamisetty, A. (2019). Big Data Engineering for Real-Time Inventory Optimization in Wholesale Distribution Networks. Available at SSRN 5267328.[CrossRef]
- Meda, R. (2021). Machine Learning-Based Color Recommendation Engines for Enhanced Customer Personalization. Machine Learning, 4(S4).